Microsegmentation – small networks, but great security

Local network segmentation is a cybersecurity topic that is discussed too little. Microsegmentation may be perceived as technically too difficult to implement. On the other hand, as services move to the cloud, it may be felt that the organization no longer needs anything other than an internet connection, so why is it still important to […]
Microsoft 365 Tutorial Video – Part 5 – Microsoft 365 Breaches

During the fall of 2025, Above IT will continue to release Microsoft 365 tutorial videos. In the fifth part of the tutorial series, Above IT ‘consigliere’ Lauri Haveri reviews the security and breaches of the Microsoft 365 environment, which the Cybersecurity Center has recently warned about. We will continue to publish similar tutorial videos monthly […]
Microsoft 365 Tutorial Video – Part 4 – Securing Microsoft 365 Environments

During the fall of 2025, Above IT continues to release Microsoft 365 tutorial videos. In the fourth part of the tutorial video series, Above IT ‘consigliere’ Lauri Haveri goes through ensuring the continuity of the Microsoft 365 environment. We will continue to publish similar tutorial videos monthly in the future – for the benefit of […]
Attack Paths and Attack Surface

Cybersecurity is more important today than ever before, and one of the key concepts in this context are attack paths and attack surface. But what do these terms actually mean and why is understanding them essential for every organization? Matias Haapaniemi explains these basics in his blog post this time. Attack Paths and Attack Surface […]
Microsoft 365 Tutorial Video – Part 3 – Hardening Microsoft 365 Environments

During spring 2025, Above IT will release a series of tutorial videos on Microsoft 365 technologies. In the third part of the tutorial series, Above IT ‘consigliere’ Lauri Haveri goes through the basic hardening of the Microsoft 365 environment, which the cybersecurity agency also recommends reviewing! We will continue to release similar tutorial videos monthly […]
Recording: Holistic Cybersecurity Webinar
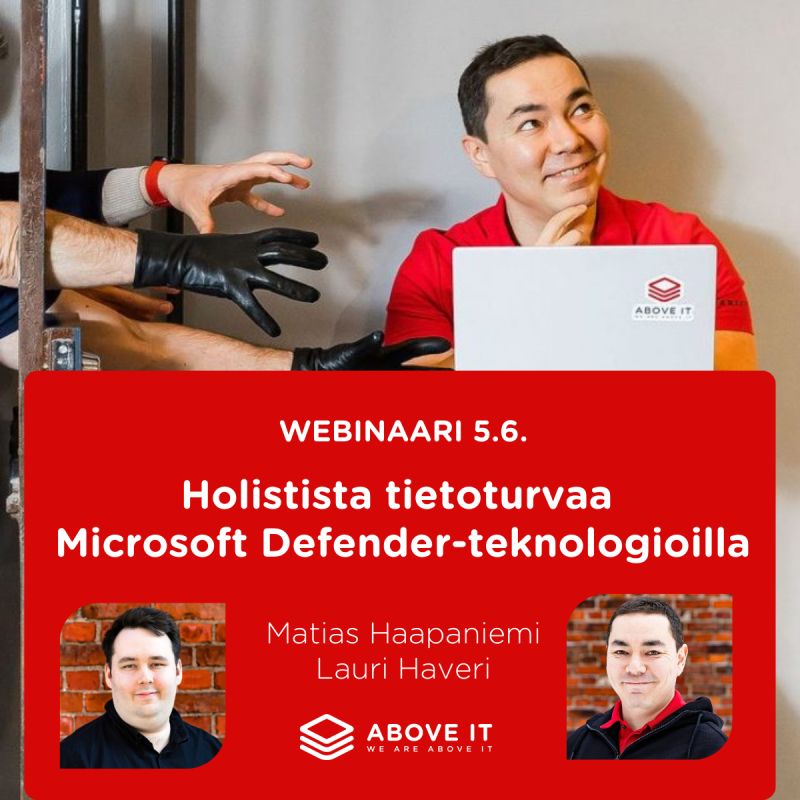
On June 5, 2025, we organized a webinar on Microsoft 365 Defender technologies and holistic cybersecurity. The topic attracted a good number of attendees. Did you miss the webinar? Rest assured, you have come to the right page. Continue reading. Defender Technologies for Holistic Cybersecurity? Did you know that Microsoft, with its Defender technologies, has […]
Microsoft Entra Suite: Implementation Challenges

In my previous blog post, I briefly explored the capabilities of Microsoft Entra ID Governance and the identity lifecycle: Microsoft Entra Suite and the User Data Lifecycle. This time, I’ve been thinking about the challenges organizations might face when implementing the service. Integrating Microsoft Entra Suite Identity Governance (Microsoft Entra – Secure Identities and Access […]
Microsoft 365 Tutorial Video – Part 2. – Defender for Cloud Apps

During spring 2025, Above IT will release a series of tutorial videos on Microsoft 365 technologies. In the second part of the tutorial video series, Above IT ‘consigliere’ Lauri Haveri delves into Defender for Cloud Apps technology – a cloud broker service enabled by the Microsoft 365 environment, with which you can manage and protect […]
Recording: Better Data Protection Webinar

We organized a webinar on May 15, 2025, focusing on Microsoft 365 Purview technologies and better data protection. The topic attracted a good number of attendees. Did you miss the webinar? No worries, you are on the right page. Keep reading. Purview Technologies for Better Data Protection? Did you know that the majority of data […]
Browser applications securely deployed

Microsoft’s Entra Application Proxy, or App Proxy for short, securely publishes browser-based applications from the local environment. Publishing services to the public network always involves risks, which is why publishing services through a Virtual Private Network (VPN) has become an established practice. Did you know that with modern methods, you can publish applications to work […]




